Colin Nagy | March 25, 2025
The Billion Dollar Spy Edition
On tradecraft, betrayal, and modern government purges.
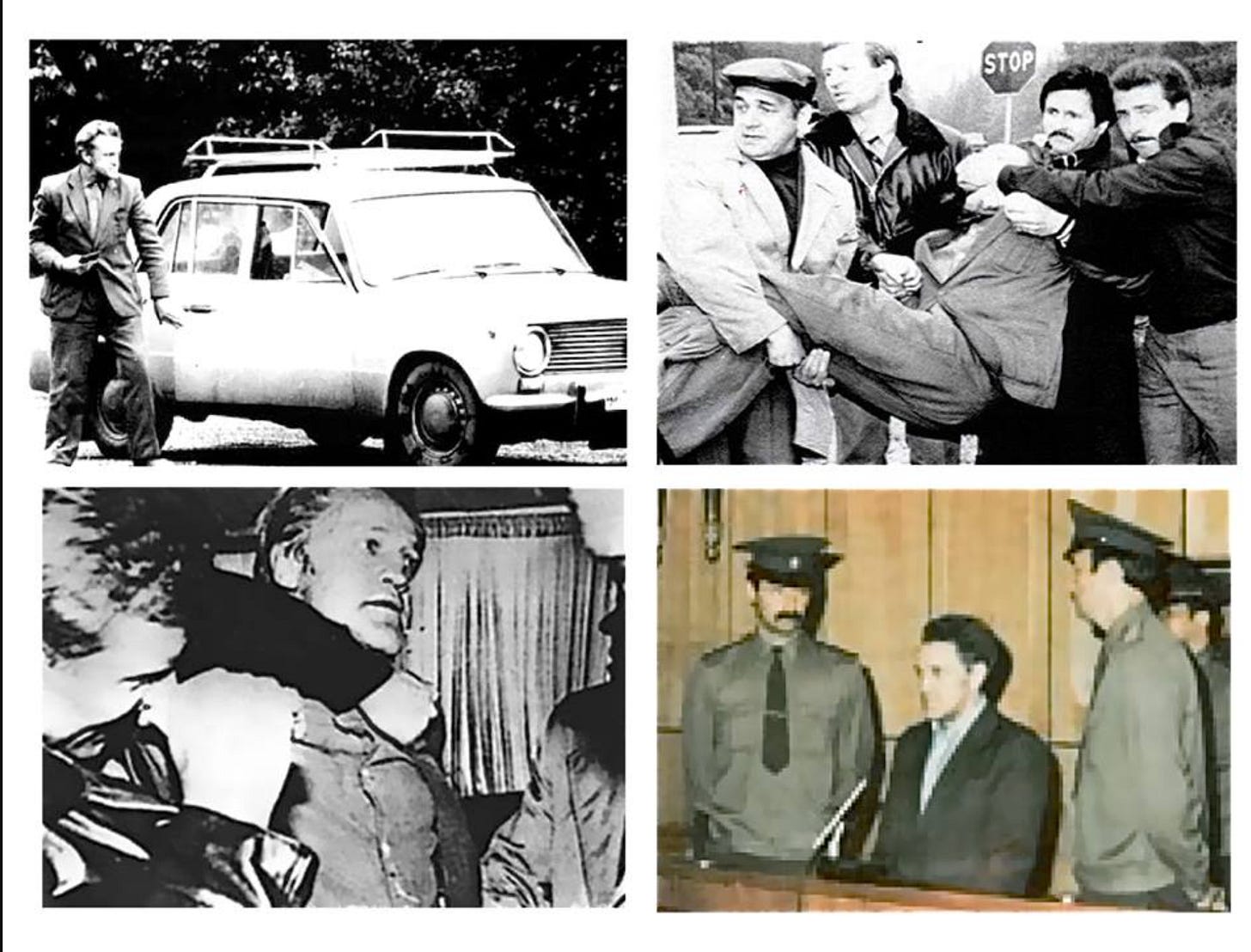
Colin here. Adolf Tolkachev pulled off the intelligence coup of the Cold War from inside the heart of Soviet military research. An engineer with access to the USSR's most sensitive radar technology, Tolkachev volunteered to spy for the CIA in 1978. Over seven years, he handed over thousands of classified documents so valuable they reportedly saved the U.S. billions in R&D costs, earning him the nickname "The Billion Dollar Spy."
Moscow was the hardest intelligence target on Earth, with KGB surveillance shadowing every American official. CIA officers navigated elaborate "surveillance detection routes" (known as SDRs) for hours before meetings, changed clothes in public bathrooms, and employed every disguise technique imaginable. It was the stuff of John le Carré novels, playing out in real life.
All the while, Tolkachev smuggled classified documents out of his monitored workplace, photographed them with CIA-supplied cameras, and returned them.
This intelligence directly influenced American F-15, F-16, and F/A-18 designs, giving the U.S. a decisive edge—stuff that even made it into Top Gun doctrine, the storied Naval dogfighting school.
His motivation? Revenge. Tolkachev’s wife's parents were victims of Stalin's purges, and this trauma, combined with his hatred of the Soviet system, compelled him to cross over.
In 1985, after seven years of flawless espionage, Tolkachev was arrested and later executed. His downfall came not from any operational mistake: Tolkachev was betrayed by an American: Edward Lee Howard, a disgruntled ex-CIA employee.
Howard had trained to join the Moscow station, where he would have helped handle Tolkachev. But the CIA fired him in 1983 after he failed a polygraph. Furious over his treatment, Howard contacted the Soviet embassy, offered his services, and betrayed Tolkachev before fleeing to Moscow.
Why is this interesting?
The Tolkachev case exposes intelligence work's most dangerous vulnerability: the insider threat.
US intelligence officers are taught the MICE framework to understand why people betray their country:
Money: Financial gain
Ideology: Belief in another system
Compromise: Blackmail or coercion
Ego: Resentment, revenge, or need for recognition
Howard's betrayal stemmed from ego and his resentment toward his former employer. This pattern repeats throughout US intelligence history, with other traitors like Aldrich Ames and Robert Hanssen causing immeasurable damage.
What makes this relevant now is the mounting counterintelligence threat in the US.
A recent AP report warns that "a mass purge of intelligence professionals under a second Trump administration could create a perfect storm for foreign espionage recruitment."
When career intelligence officers and other government workers face overnight dismissals, these MICE factors become acute risks. The core parts of the framework create vulnerabilities adversaries can exploit.
After Tolkachev's exposure, the CIA made new systems and protocols for handling dismissed employees with sensitive knowledge—including better psychological support and controlled reintegration into civilian life. (Cont.)
If you are interested in the future of autonomy, check out the Ride AI summit happening next week (4/2) in Hollywood. Ride AI is all about digging into the real work happening in AV today—what’s working, what’s still challenging, and what it takes to make driverless tech an integrated part of our world. They’re gathering a tight-knit group of CEOs and other leaders in autonomous vehicles and AI-driven hard-tech for an exclusive experience, emphasizing meaningful discussions, inspiring presentations, and in-depth networking.
WITI subscribers can save 50% on tickets this week by registering here: https://ti.to/rideai/ride-ai-2025/with/witi-x-ride-ai
The lesson: A resentful ex-employee with classified knowledge represents an existential counterintelligence threat. It is worth noting that there is nuance here—a lot of classified knowledge ages out quickly, and there are systems for compartmentalizing information.
But information on technology, operational protocols, IP, and even other seemingly unsexy things all have value for adversaries.
Russia, China, Iran and many others are increasingly sophisticated with both technology (China is still up in US telecoms through the Salt Typhoon attack) and old-school human intelligence. And now, they are facing an unprecedented opportunity. (CJN)